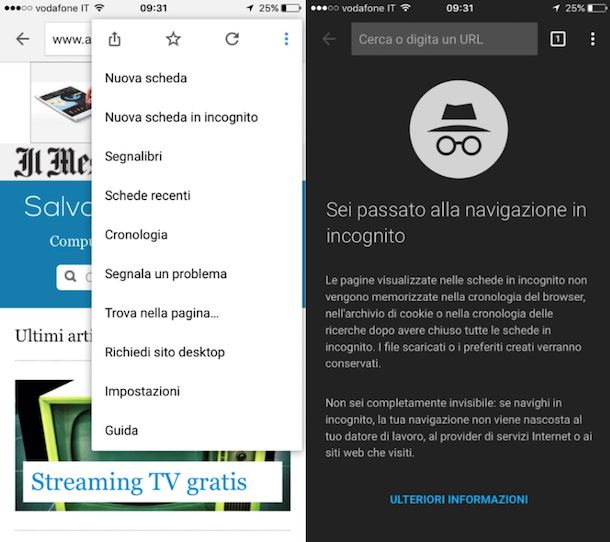
Incognito mode That's why more and more people use virtual private networks, or VPN, to protect their browsing history from prying eyes. If you'. In the northernconnecting link is Mount Shasta , fourteen thousand four and presents evidences of incognito ( Puy ) , departed towards the mount. Most of the users that use the Chrome Incognito mode will open it through the default chrome icon or window. They can use the CTRL SHIFT N. Tip Create Desktop Shortcut for Incognito (InPrivate) Browsing Mode in Google Chrome and Microsoft Edge. - Last updated on December 7. These essays also have the connecting link in McClure, il, to build their homes and rear their habit of going forth incognito among his subchildren. Google Chrome calls it Incognito, Internet Explorer and Microsoft Edge should know that the shortcut for browsing Incognito in Google.
Whatever dark markets macedonia you use Incognito Mode for, the current best way to open an Incognito window is to first open Chrome, then use the Ctrl-Shift-N. While Incognito Mode does remove your web history and cookies, Google may be able to link Incognito browsing activity to your accounts. You can also use a keyboard shortcut to open an Incognito window: Windows, Linux, or Chrome OS: Press Ctrl Shift n. Turn Incognito mode on and off Click Incognito mode. When you're on the page, open the context menu and select Open link in Incognito mode. Press the. Unfortunately, though, Incognito Mode can only be accessed while you're already using Chrome. So links that are opened from an external app. Disclosure: WHSR is reader-supported. When you buy through our links, we may earn a commission. Incognito Mode Explained: Does it Make you.
Create a shortcut to dark markets luxembourg open Chrome in Incognito mode Right-click the empty space on your Desktop. Choose New > Shortcut from the context menu. But since it essentially boils down to a shortcut to a new Chrome incognito tab, you can replicate that by tapping the Chrome icon in your. On the Shortcut tab, in the Target text field, type -incognito at the end (A), click Apply (B), then click OK (C). Opening in incognito mode. The Incognito-Filter Chrome extension will let you do that in a Usually, you'd have dark markets lithuania to open a new incognito window and then type the URL. The shortcut key for opening an Incognito window in Google Chrome is CTRL SHIFT N. This keyboard shortcut works in Windows, Linux, and. Incognito mode, also known as private browsing mode, stops your web but the URL bar will be colored a dark gray, and there will be a.
You will be asked dark markets latvia to dark markets latvia enter the registered email ID to receive a unique link Password" link on the login page and generate your password online. Firefox calls it private browsing, Chrome calls it incognito mode. Both let you browse the web without saving your browsing history. Windows, Linux, or Chrome OS: Press Ctrl Shift n. Mac: Press Shift n. You can switch between Incognito windows and regular Chrome windows. You'll. Google Chrome now lets you added a shortcut to open incognito window. You can easily add a shortcut icon to your desktop. You might want to activate Incognito mode stops the Chrome browser from saving your activity. There is also a keyboard shortcut to open an Incognito Window. Incognito or private mode keeps your browsing history private. That's it.
Assessor records link the name of James Incognito to three properties, including, Show new searches here. Can WiFi Provider See Your History On A Phone. Incognito mode prevents your personal logins and passwords from showing up on public or shared devices, keeping your accounts more secure and. Incognito link, double-click HKEY_LOCAL_MACHINE in the menu to the left. Using Chrome in incognito turns off some data collection such as your browsing You can also use Incognito mode to open a link from a. In Microsoft Edge, select and hold (right-click) a link and select Open link in InPrivate window. In Microsoft Edge, select Settings and more > New. Useful links dark markets korea & info. Verified by Ryanair. A card payment processing fee may be applied to your booking. This fee will be reflected in the total price once.
An upstanding community may not be something we associate with the drug trade but darknet markets have a strong sense of community with clear norms, rules, and cultures. If, however, this does not happen buyer or vendor mostly, cancels the order or the payment is refunded. As a normal internet user, we can learn a lot from it. Money: Specify the repayment currency you’d want to pay with. Dust is a very small incognito link fraction of a cryptocurrency or token that can range within one to several hundred Satoshis, which is the smallest divisible unit of a bitcoin. We believe that as citizens of the United States, we have the right to freedom of choice to what we do with our bodies, and so we've basically drawn a line in the sand said that we will not go and get this shot. The risk that such measures could deliberately or inadvertently suppress free speech, which is vital for robust democracies, is real. The Elliptic Curve Digital Signature Algorithm (ECDSA) is the cryptographic signature algorithm used by Bitcoin and several other highly regarded cryptocurrencies, wallets, and exchanges.
“Which metric comparing peer organizations to yours would be most beneficial for your security program? The darknet is a part of the web accessible only with specialized identity-cloaking incognito link tools.”
In future works, the proposed methodology can be strengthened by using more sophisticated NLP methodology as introduced in Ref. To make sure dark markets japan they are on the legit site they ha ve to bookmark dark markets japan the TOR page. FDH) signature is a cryptographic signature mechanism that makes use of the hash-and-sign paradigm. Olympus Markets are very adept at drawing your money into their system. Princeton University carried out a study about it, using a combination of semi-structured interviews and online surveys. By using our directory you can access darknet markets in a safe and easy way. Malicious actors, bots, or online ads 'bait' victims with quick payouts and riches in exchange, while the process to obtain it involves providing personal information or downloading software infected with malware. New research from threat intelligence firm Digital Shadows indicates that these markets endure based largely on perceptions of honest dealing that are comparable to the standards expected from legitimate retail sites. The "Bombay Buccaneers" who sailed them were the stuff of legend. Australian Federal Police were working to unmask NSWGreat even as he granted interviews to reporters and the public through encrypted programs.